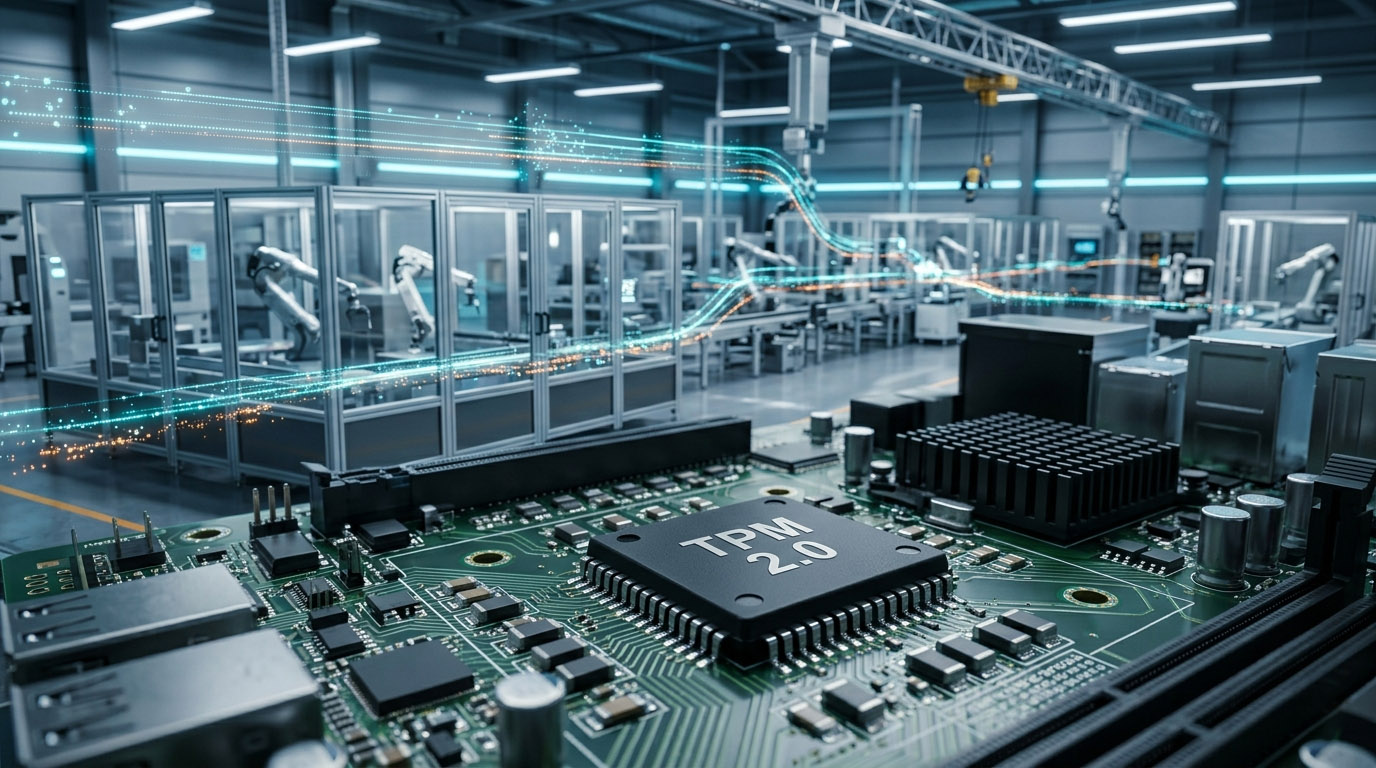
When people hear TPM, many first think of Total Productive Maintenance in manufacturing. However, in the industrial security field, TPM (Trusted Platform Module) — a hardware security chip — also plays an irreplaceable role.
It is not exclusive to consumer PCs. Instead, it is a core component for securing Industrial Internet of Things (IIoT) and Industrial Control Systems (ICS).
It provides a solid hardware-based trust foundation for smart manufacturing and industrial digital transformation, with wide and critical applications in the industrial sector.
1. Core Application Scenarios of TPM in Industry
TPM’s applications in industrial scenarios always revolve around security. It covers the entire process from device startup and data transmission to production control, adapting to security needs of different industrial environments.
1.1 Industrial Control System Security Protection
Industrial control systems serve as the “brain” of factory production, where security directly dictates operational uptime. In this critical environment, TPM acts as a “security gatekeeper.” By verifying the signatures of BIOS, Bootloader, and operating systems in controllers like Siemens and Schneider, TPM 2.0 builds an unalterable chain of trust. This mechanism effectively prevents malware from invading through firmware vulnerabilities. Taking automotive production lines as an example, TPM combines with UEFI SecureBoot to protect PLC programs. If an abnormality is detected, it immediately halts device startup to block targeted APT attacks.
1.2 Industrial Edge Devices and IIoT Security
As IIoT adoption grows, a massive number of edge devices—such as gateways and sensors—connect to industrial networks. To secure these potential weak links, TPM provides a comprehensive defense layer. Industrial gateways establish trusted connections via unique Endorsement Key (EK) certificates. Such a strategy ensures isolation between OT and IT networks, preventing the spread of cyberattacks. Furthermore, industrial data collected by smart sensors is encrypted using keys stored within the TPM. This protects sensitive production parameters from theft or tampering during transmission.
1.3 Industrial Automation and Smart Manufacturing
The core of smart manufacturing is “security and controllability.” To achieve this, TPM provides full-lifecycle protection for automated equipment. In the field of industrial robotics, the module secures motion control instructions to prevent hackers from causing physical production accidents. Simultaneously, it safeguards core algorithms and proprietary processes built into the robots to prevent intellectual property theft. For highly sensitive data like design blueprints, TPM utilizes hardware encryption. Even if a device is physically stolen, unauthorized personnel cannot access the core data stored within.
2. Special Requirements and Implementation Methods of Industrial TPM
Compared with consumer-grade TPM, the harsh environment and high security requirements of industrial scenarios put more stringent demands on TPM. Its implementation methods also differ.
Features | Industrial TPM Requirements | Consumer-Grade TPM Differences |
|---|
Operating Environment | Wide temperature range (-40°C~85°C), vibration resistance, electromagnetic interference resistance, suitable for harsh factory environments | Room temperature environment (0°C~40°C), no special anti-interference design, suitable for home and office scenarios |
Certification Standards | Must pass industrial-grade security certifications such as IEC 62443, AEC-Q100 (automotive grade), and FIPS 140-3 | Mainly complies with PC client standards, with relatively low security certification levels |
Deployment Form | Mostly dTPM (discrete TPM), some integrated into industrial CPUs to ensure higher security | Mainly fTPM (firmware TPM), such as Intel PTT and AMD fTPM, focusing on cost control |
Connection Method | Supports industrial bus interfaces such as CAN Bus, adapting to industrial device connection needs | Mainly connected to the motherboard through LPC or SPI interfaces, adapting to PC devices |
Currently, industrial-grade TPM chips (such as ST33KTPM and Infineon SLB9673) are designed specifically for harsh industrial environments. They pass high-level security certifications such as FIPS 140-3. They can stably provide hardware-level encryption and key management capabilities to meet the long-term operation needs of industrial scenarios.
3. Difference Between TPM (Trusted Platform Module) and TPM (Total Productive Maintenance)
Due to the same abbreviation, many people confuse the two TPM concepts. They belong to different fields and have completely different core functions and application goals. The specific differences are as follows:
Comparison Items | Trusted Platform Module (TPM) | Total Productive Maintenance (TPM) |
|---|
Full Name | Trusted Platform Module | Total Productive Maintenance |
Field | Computer/Industrial Security Field | Equipment Management/Production Maintenance Field |
Essence | Hardware security chip/firmware, providing security protection capabilities | Management system/work method, optimizing equipment management |
Core Functions | Encryption, key management, secure boot, integrity verification | Full-lifecycle equipment management, preventive maintenance, efficiency improvement |
Application Goals | Prevent data leakage, system tampering, and cyberattacks; ensure industrial security | Reduce equipment failure rate, improve OEE (Overall Equipment Efficiency), and enhance production efficiency |
Typical Applications | Industrial controllers, edge gateways, smart sensors, power equipment | Production line equipment maintenance, factory equipment management systems, production efficiency optimization |
4. Core Value of Industrial TPM
TPM’s applications in the industrial field are not just simple security protection. It can bring multi-dimensional value to enterprises and support industrial digital transformation.
1. Hardware-based trust foundation: TPM provides unalterable secure boot and identity authentication. It becomes the “root of trust” for industrial system security, resisting malicious attacks from the source.
2. Compliance guarantee: It helps enterprises meet industrial security standards and data protection regulations. It avoids risks such as fines and production suspension due to non-compliance.
3. Reduce security risks: It prevents production interruptions and safety accidents caused by device tampering and data leakage, reducing economic losses for enterprises.
4. Support industrial digital transformation: It provides a security foundation for OT/IT integration, IIoT, and smart manufacturing. It breaks security bottlenecks and promotes the application of new technologies in industrial scenarios.
5. Specific Impacts of TPM on Industrial Use
The deployment and application of TPM have a profound impact on industrial production, enterprise operations, and technological upgrading. It has both positive driving effects and a few potential issues that need to be avoided. The details are as follows:
5.1 Positive Impacts: Fully Empower Industrial Security and Efficiency
(1) Ensure production continuity: By protecting industrial control systems and equipment, TPM effectively avoids production downtime caused by malicious attacks and firmware tampering. Especially in continuous production industries such as automotive manufacturing, the chemical industry, and power, it can significantly reduce downtime losses and ensure stable production.
(2) Improve data security: Industrial data is the core asset of smart manufacturing. TPM protects sensitive data such as production processes and equipment parameters through hardware encryption. It prevents data leakage and tampering, providing a security guarantee for data-driven production optimization.
(3) Reduce enterprise security costs: Although deploying industrial-grade TPM will increase equipment costs initially, it can reduce huge losses caused by security accidents and data leakage. It also reduces long-term security operation and maintenance costs, with outstanding cost-effectiveness in the long run.
(4) Promote industrial digital transformation: The development of OT/IT integration and IIoT is inseparable from a secure equipment and network environment. TPM solves the security pain points of edge device access and data transmission, clearing obstacles for digital transformation.
(5) Enhance enterprise market competitiveness: Against the backdrop of increasingly strict global industrial security requirements, deploying TPM can improve enterprises’ security compliance capabilities. It enhances customer trust in products and services and boosts market competitiveness.
5.2 Potential Impacts: Issues That Need to Be Reasonably Avoided
(1) Increased initial deployment costs: Industrial-grade TPM chips are more expensive than consumer-grade products. Upgrading old industrial equipment to adapt to TPM also requires hardware upgrades, which will increase enterprises’ initial investment.
(2) Increased operation and maintenance complexity: TPM key management and firmware updates require professional technical personnel. This places higher requirements on enterprises’ IT operation and maintenance capabilities, and small enterprises may face operation and maintenance pressure.
(3) Compatibility issues: Some old industrial equipment and control systems have poor compatibility with TPM 2.0. Compatibility testing and adaptation modifications are required; otherwise, it may affect the normal operation of the equipment.
Overall, the positive impacts of TPM on industrial use far outweigh the potential issues. Through reasonable selection, phased deployment, and professional operation and maintenance, these issues can be effectively avoided, and its security value can be fully exerted.
6. Industrial TPM Application Cases
The following practical cases can more intuitively reflect the application value and actual impact of TPM in the industrial field:
1. An automotive parts enterprise: After deploying a firmware security solution based on TPM, it successfully prevented attackers from stealing core production processes by tampering with robot control programs. It avoided tens of millions of economic losses, ensured the continuous operation of the production line, and improved production efficiency.
2. Huaneng Ruiwo T1316TR DCS System: Adopting localized design and integrating TPM security chips, it provides a trusted computing environment for power generation control systems. It not only eliminates security risks caused by foreign software and hardware monopolies but also meets the high security and high reliability requirements of the power industry, ensuring stable power supply of the power grid.
3. A large international chemical enterprise: Deployed TPM-protected industrial control systems in factories around the world. It realized unified security management of production equipment distributed in different countries. It not only met the data protection regulations of various countries but also reduced global industrial security risks and improved the enterprise’s security management efficiency.
7. Conclusion
TPM applications in the industrial sector have long surpassed the limitations of “consumer-grade security,” evolving into a critical infrastructure for smart manufacturing. By providing hardware-level protection for equipment, control systems, and data transmission, this technology ensures production continuity while significantly enhancing compliance and risk mitigation.
A crucial distinction must be made between “Trusted Platform Module (TPM)” and “Total Productive Maintenance (TPM)” to prevent conceptual confusion during technology selection. As Industry 4.0 continues to advance, industrial security requirements will only intensify, positioning TPM as an indispensable security component for the modern digital landscape.
💡 Frequently Asked Questions (FAQ)
Q: Why is hardware-based security (TPM) better than software-based security?
A: Software can be bypassed if the Operating System is compromised. TPM is a physical chip isolated from the CPU; it performs cryptographic operations in a “secure vault” that hackers cannot easily access via the network.
Q: Can TPM 2.0 help with remote maintenance security?
A: Yes. It provides a unique hardware identity for the machine, ensuring that only authorized remote engineers can access the controller via a secure, encrypted tunnel.
Q: Is TPM mandatory for Smart Manufacturing?
A: While not always legally mandatory yet, it is becoming a de facto requirement for insurance compliance and tier-1 supply chain participation in the EU and North America.
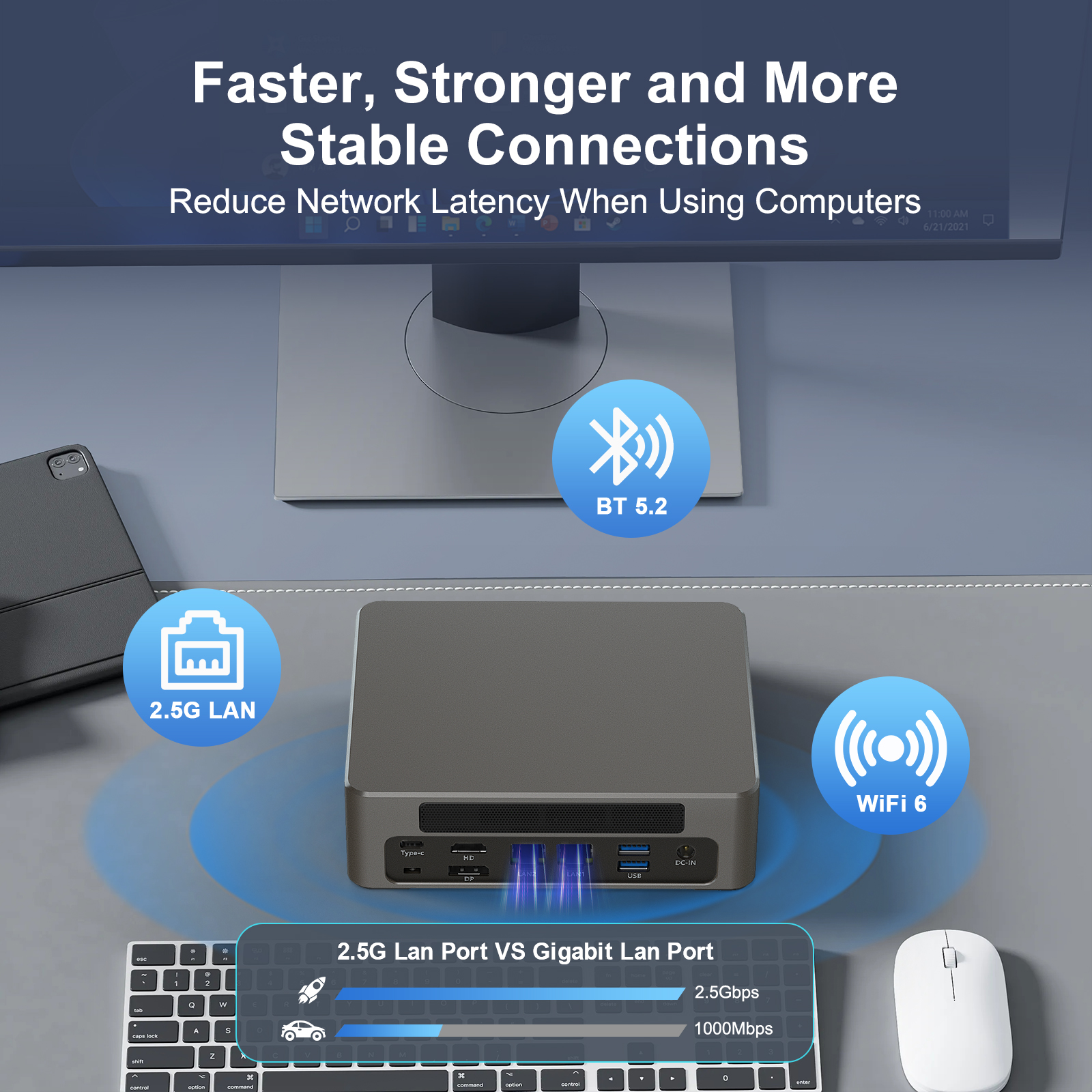
HYSTOU has established its R&D headquarters in Shenzhen, drawing on over a decade of experience. Our core team members, who previously served at renowned companies such as Inventec and Quanta Computer, form the backbone of our technical expertise. With robust R&D and innovation capabilities, we remain steadfast in our commitment to pursuing excellence in the field of technology products.